Geopolitical tensions are heightening across multiple regions. Historically, moments like this come with an increase in cyber activity. While that doesn’t always translate into sophisticated attacks against businesses, it can create more noise in the cyber space and a rise in opportunistic threats.
For brokers and businesses, it’s natural to wonder whether this means greater risk. The overall threat profile for SMEs remains stable, but the nature of activity continues to evolve – and understanding that difference is key. As always, the most effective defense remains strong cyber hygiene.
What we’re currently seeing
Across the global digital environment, we’re seeing a blend of low-level disruption and opportunistic activity. That includes public-facing websites and online services experiencing interruptions, while threat groups look to push themed messaging online.
Attribution is often unclear during these periods, and much of the activity is broad rather than targeted. This generates an uplift in background cyber “noise”. This noise can trigger claims activity and draw media attention, but it rarely represents a shift towards high-impact, targeted attacks against businesses.
The types of threat activity that typically increase
In periods of geopolitical tension, we usually see a familiar pattern play out. Instead of sophisticated attacks, it’s high-visibility, low-effort activity that grabs attention and fuels headlines. That includes:
- Politically motivated website defacement
- DDoS attacks against public-facing websites
- Hack-and-leak extortion using geopolitical branding
- Conflict-themed phishing (such as, crisis-style emails or SMS alerts or social media campaigns)
- False or exaggerated breach claims amplified online
These campaigns exploit uncertainty and attempt to pressure individuals or organizations into reacting quickly. While disruptive, they are typically unsophisticated, short-lived and not designed to cause major operational damage to SMEs.
What this means for businesses
Despite the increase in global instability, the direct risk to businesses remains consistent with what we’ve historically observed.
Targeted, strategic cyber activity often focuses on government adjacent entities, critical infrastructure, or organizations operating within affected regions. For small to mid-sized businesses, the more realistic exposure comes from opportunistic threats – phishing, credential attacks and unpatched vulnerabilities – rather than advanced cyber operations.
Indirect disruption remains possible, including supply chain issues or instability in services linked to affected regions. But key indicators show that incident volumes for most businesses remain normal.
What should businesses do?
While the overall risk hasn’t fundamentally changed, periods of instability are a useful reminder to double down on the essentials. The vast majority of successful opportunistic attacks exploit simple gaps.
We recommend to:
- Monitor unusual behavior in email accounts and check for signs of compromise.
- Run endpoint detection and response (EDR) tools and review logs for suspicious activity.
- Keep software and internet-facing services patched and up to date
- Ensure MFA is enabled wherever possible
- Maintain regular employee phishing awareness
- Review and test incident response plans
- Validate the source of any appeal or campaign
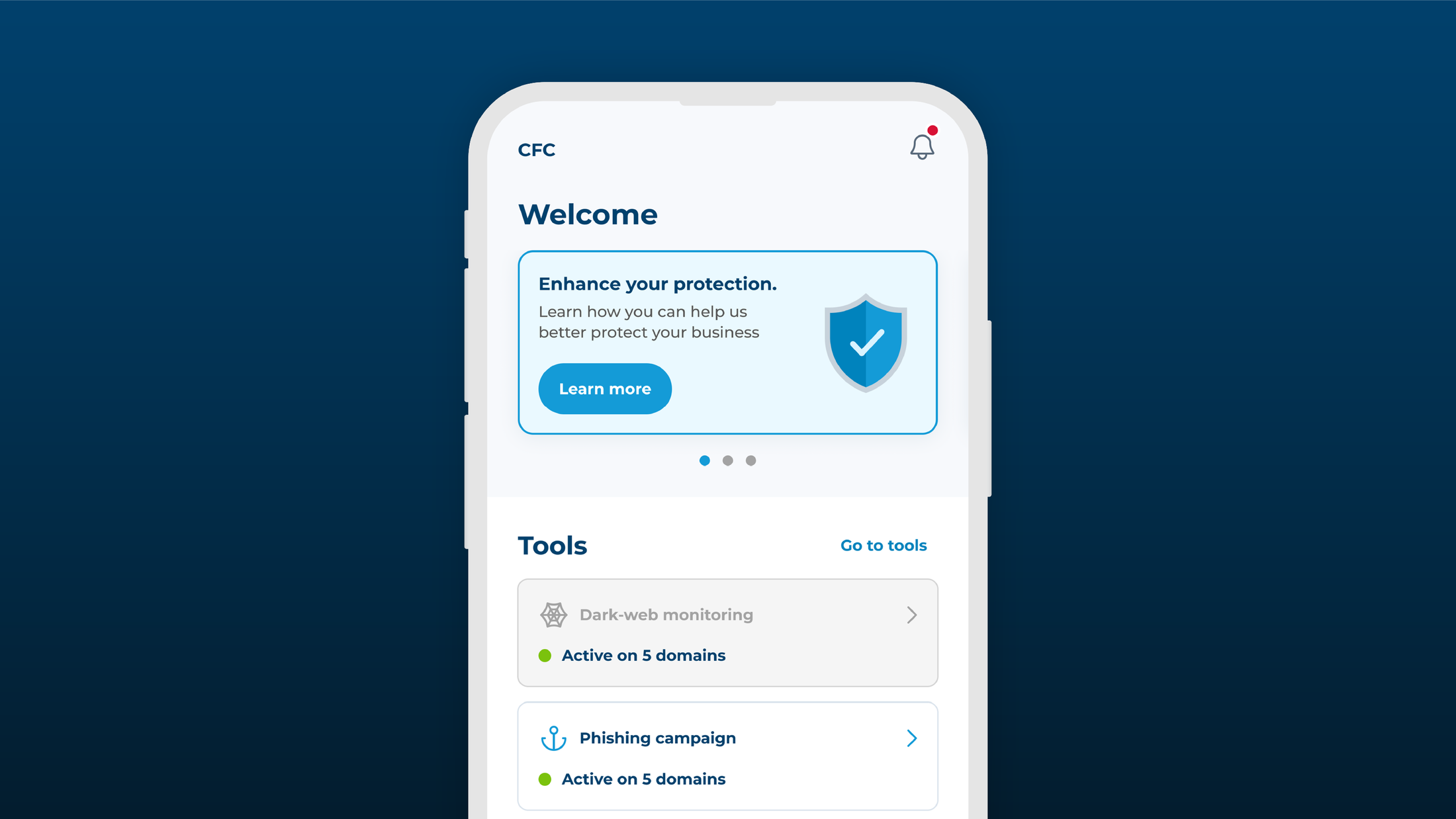
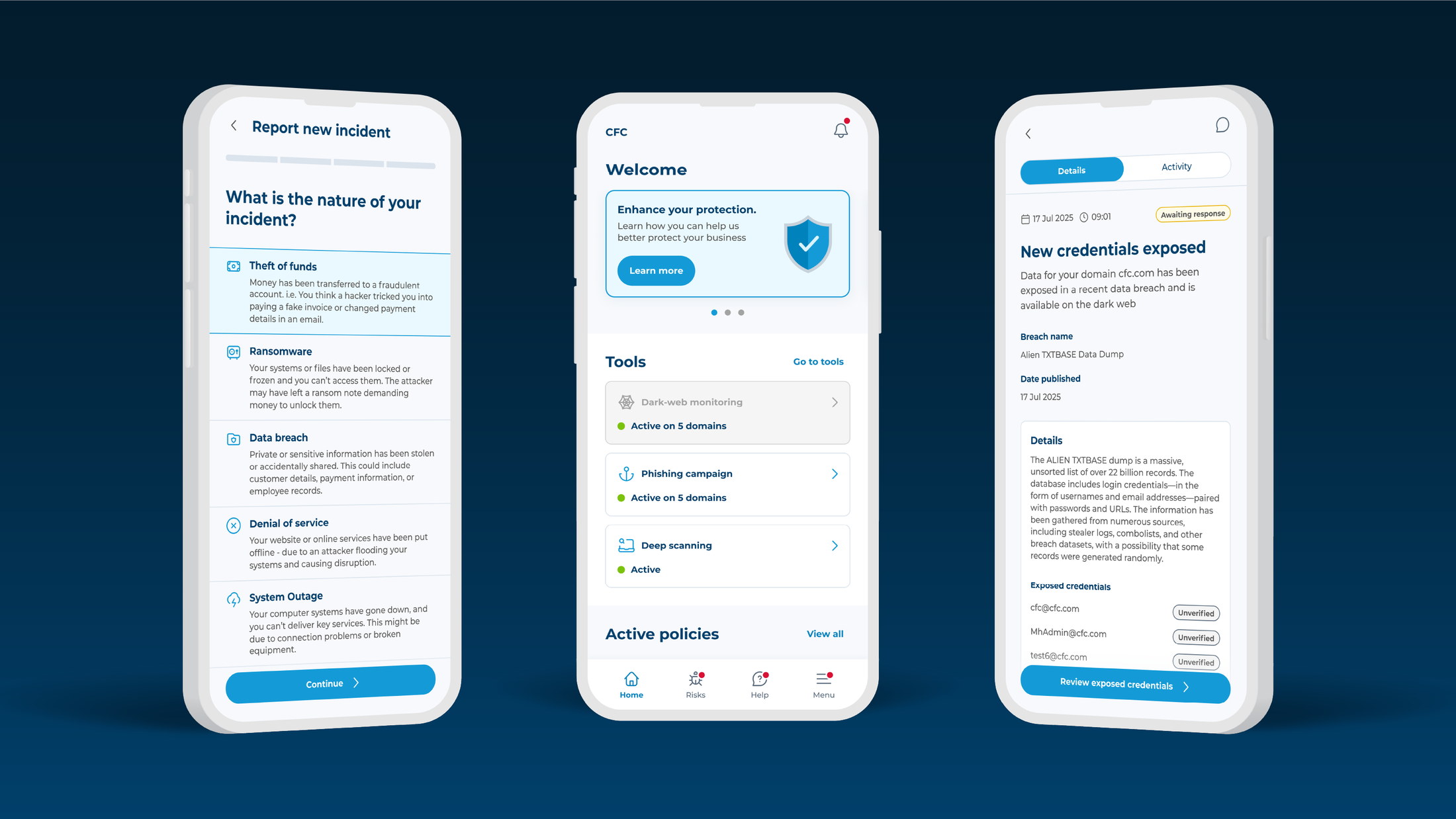
CFC monitoring & support
CFC’s proactive cyber team is monitoring the situation. Our priority is to help insureds prevent incidents before they occur.
If you are a policyholder and have questions or need support, please contact our cyber response team via the Response app, our website or at customersupport@cfc.com. If you’re a broker, get in touch with any questions.
Meet the author
Jason oversees our proactive and global security services, driving our global strategy, strengthening security capabilities and unifying incident response teams to deliver a seamless, world-class security service.