A recent cyber incident has affected Instructure’s Canvas platform, following unauthorized access linked to its “Free‑For‑Teacher” environment and an extortion campaign by the threat group ShinyHunters.
While the incident is generating significant attention, the risk to most organizations appears driven by a threat-actor leak site and public messaging.
As the situation continues to develop, we’re monitoring threat activity and leak-site postings for our insureds, and recommend key practical steps to reduce exposure.
What's happened
In late April 2026, threat actors infiltrated parts of Instructure’s Canvas, a leading cloud-based education platform used by schools, universities and businesses.
On 1 May, Instructure confirmed the incident and launched an investigation. Shortly afterwards, the threat group ShinyHunters claimed responsibility, listing Instructure on its dark‑web leak site and threatening to release data.
In the following days, the group escalated its campaign through leak‑site postings and limited disruption to some login pages, using deadlines and public messaging to apply pressure.
Who is ShinyHunters?
ShinyHunters is a financially motivated cybercriminal group active since 2019. They are known for “pay or leak” extortion, stealing data from large platforms and threatening public release rather than deploying ransomware encryption.
The group frequently targets high volume, cloud-based service providers to impact many downstream organizations at once.
ShinyHunters has been linked to previous notable data breaches such as the Snowflake incident in 2024, and the Salesforce extortion campaigns in 2025.
Who is impacted and what are the risks?
The incident primarily affects organizations using Canvas, including:
Schools, colleges and universities
Training providers and education platforms
Any organization using Canvas “Free‑For‑Teacher” environments
The threat group operates a leak site on the dark web, where it names organizations it claims to have data from. Being listed may indicate potential exposure, but it does not confirm the scope or accuracy of any data involved. Equally, not being named does not mean an organization is unaffected.
If affected, the impact may include:
Increased risk of targeted phishing or social engineering
Regulatory or notification considerations, depending on jurisdiction
Reputational and operational impacts for education providers
Key actions for businesses
We recommend Canvas users to:
Reset Canvas passwords and avoid reusing them across other systems
Invalidate active sessions and enforce re‑authentication
Enable multi‑factor authentication, particularly for admin accounts
Heighten awareness of phishing and social‑engineering attempts
Review the types of data stored in Canvas, especially sensitive information
By following these steps, organizations can reduce the risk of follow‑on activity while investigations continue.
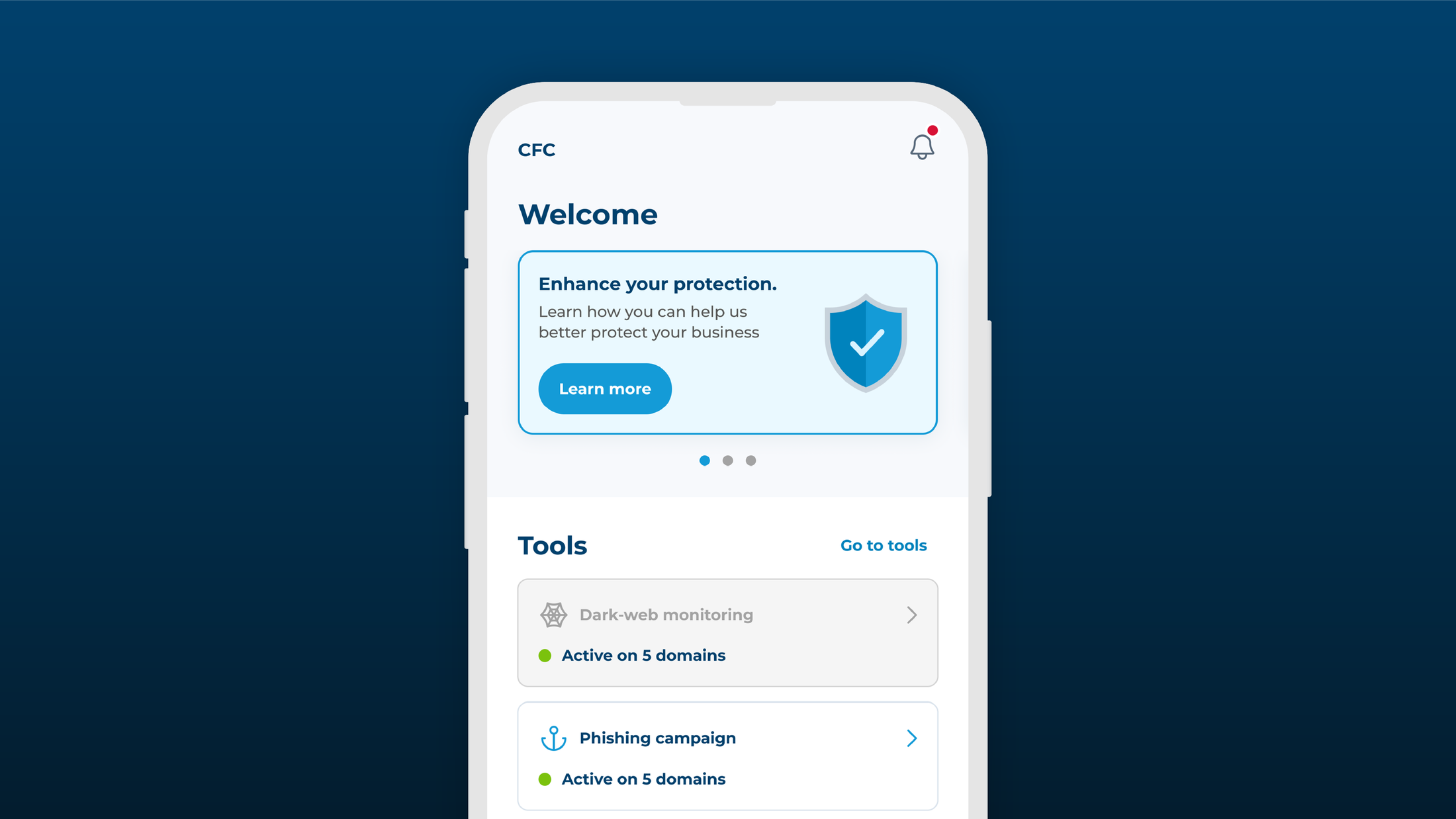
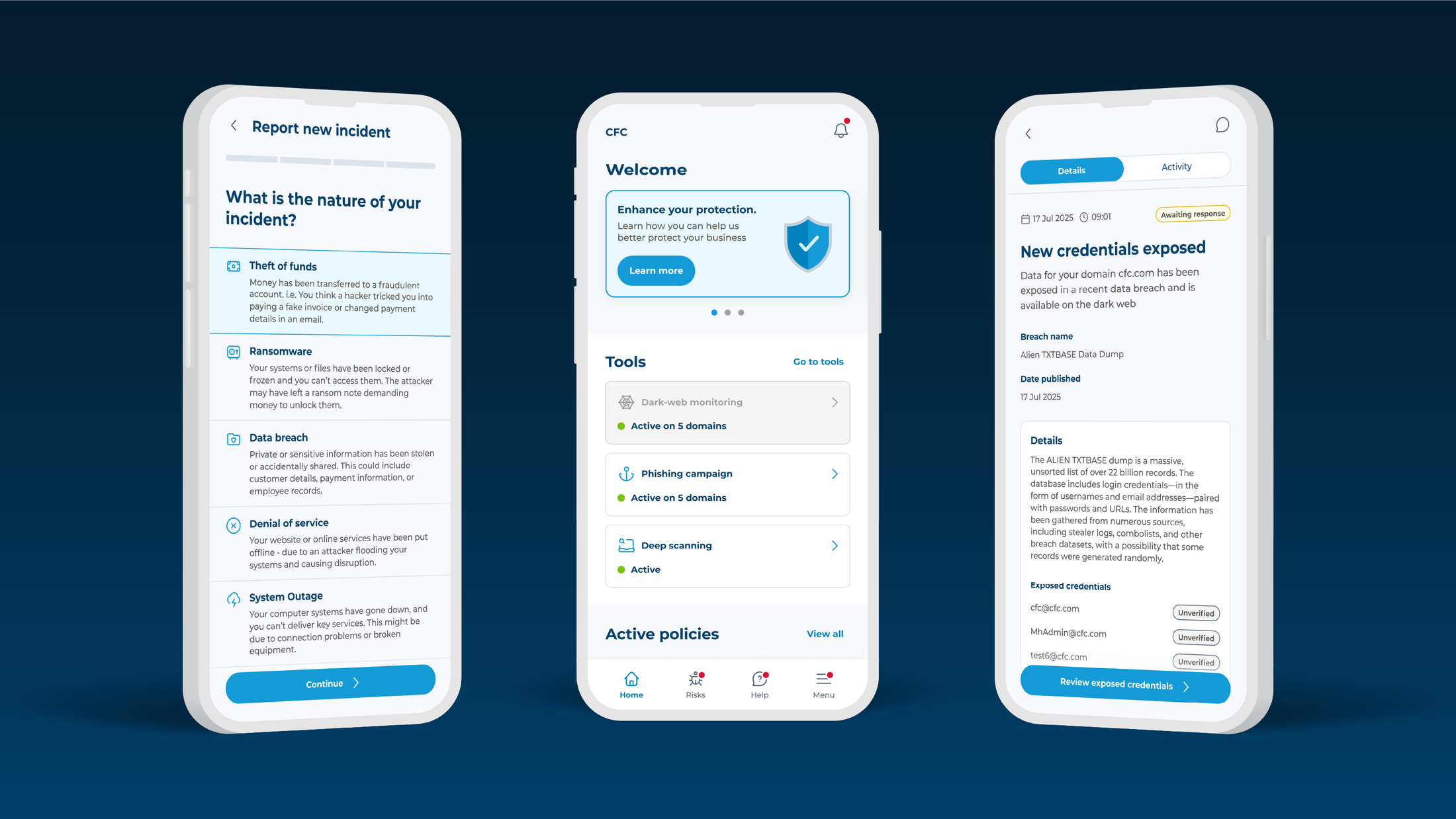
CFC monitoring & support
CFC’s cyber security and incident response teams are actively monitoring the situation and working with insureds to ensure they understand their exposure.
We will continue to:
Monitor the situation and threat‑actor activity
Review leak‑site postings on behalf of insureds
Coordinate technical, legal and claims support where required
Provide pragmatic guidance aligned to the evolving facts of the incident
The prevailing message is to remain calm. We advise a calm, fact-based approach that focuses on confirmed information, and to notify CFC early where there are concerns or indications of impact.
If you have questions or need support, please contact our cyber response team via the Response app, our website or at customersupport@cfc.com.